How Can a Secure POS Ensure Safe Financial Deals
Core Security Technologies in Secure POS Systems
End-to-End Encryption for Data Protection
End-to-end encryption (E2EE) is a crucial technology for safeguarding sensitive customer information within secure POS systems. It ensures that data, such as credit card details, is encrypted from the point of capture until it reaches the payment processor, thereby preventing unauthorized access along the way. This level of security is essential in preventing data breaches which are a common threat to businesses. For instance, it is reported that 60% of small businesses shut down after experiencing a cyber attack, highlighting the critical need for robust protection measures ("What are the security features of a modern POS system?" May 31, 2024). The encryption process involves using cryptographic algorithms that convert data into unreadable formats, maintaining the data's integrity and confidentiality throughout its journey.
EMV Chip Technology: Beyond Magnetic Stripes
EMV chip technology, developed by Europay, MasterCard, and Visa, is pivotal in reducing card-present fraud by generating unique transaction codes during each use. Since its adoption in the U.S., card-present fraud has declined by an impressive 76% ("POS Security: 11 Best Practices For Running A Tight Ship In 2024"). This shift from the vulnerable magnetic stripe to the more secure chip technology significantly heightens security measures by making it much harder for fraudulent activities to succeed. Compliance with EMV standards is, therefore, a critical step for merchants to ensure enhanced card security and maintain consumer trust.
Tokenization: Replacing Sensitive Data
Tokenization is a salient security feature in modern POS systems that involves replacing sensitive card information with non-sensitive tokens. This technique drastically reduces the impact of data theft as the actual card details are never stored within the system, and the stolen tokens are useless to cybercriminals. According to industry reports, adopting tokenization practices can not only enhance data security but also streamline compliance with PCI requirements, minimizing the scope and complexity of compliance efforts ("POS Security: 11 Best Practices For Running A Tight Ship In 2024"). By deploying tokenization, businesses can fortify their defenses against fraud and ensure a safer transaction process for their customers.
Compliance & Standards for POS Security
PCI DSS Requirements for Safe Transactions
The Payment Card Industry Data Security Standard (PCI DSS) is vital for securing transactions in POS systems. It encompasses a set of security requirements designed to protect cardholder data. Studies show that companies adhering to PCI DSS are 48% more likely to avoid breaches, indicating its importance for business security. To achieve PCI compliance, merchants must follow several steps:
- Secure Network Maintenance: Utilize firewalls and other security technologies to protect networks from unauthorized access.
- Cardholder Data Protection: Encrypt transmission of cardholder data across open, public networks to ensure data safety.
- Access Control Implementation: Limit data access based on job need; use unique IDs and multifactor authentication.
- Vigilant Monitoring and Testing: Regularly monitor networks and test security systems to detect potential vulnerabilities.
- Information Security Policy: Establish and maintain an extensive policy to address data security across the organization.
These guidelines not only shield businesses from financial losses but also safeguard reputational credibility by proving commitment to secure payment processing.
Role of SSL/TLS in Secure Payment Gateways
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols are crucial for encrypting data between POS systems and servers. These protocols play a significant role in preventing man-in-the-middle attacks, thereby securing the communication channel during transactions. SSL/TLS encryption ensures the confidentiality and integrity of transmitted data, bolstering consumer trust in digital transactions. Moreover, SSL-secured sites are favored by search engines, improving SEO rankings and enhancing business visibility online. The adoption of SSL/TLS is integral to maintaining secure payment gateways, underscoring their importance beyond just encryption—fostering a safe environment for online commerce. Secure payment gateways leverage these protocols, offering peace of mind to consumers and businesses alike, ensuring that cyber threats are mitigated through robust encryption practices.
Secure POS Hardware Infrastructure
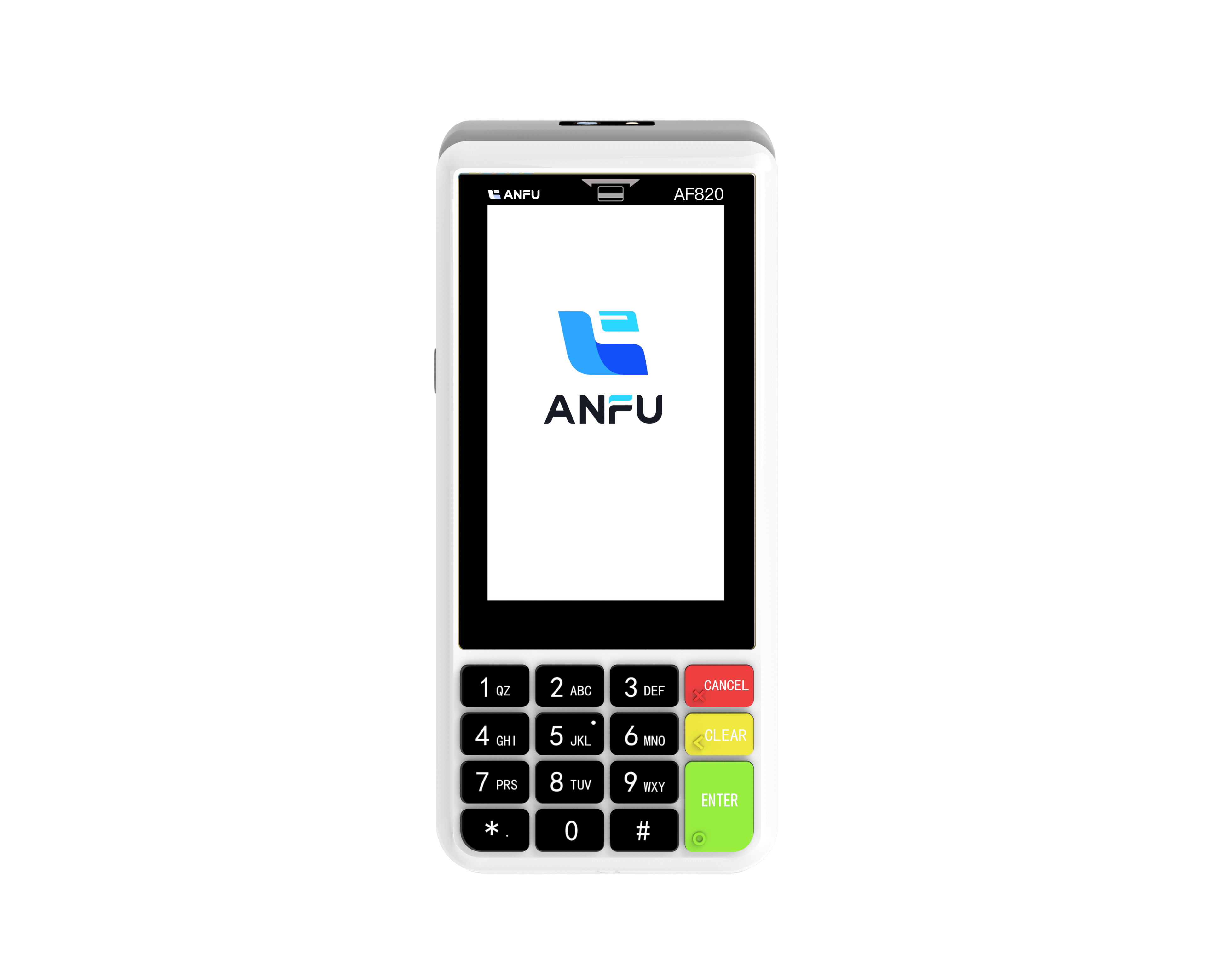
Smart Android POS Machines for Modern Retail
Smart Android POS machines are transforming modern retail by offering user-friendly interfaces, extensive app capabilities, and seamless payment integrations, revolutionizing the customer experience. These devices allow retailers to customize their operations efficiently through Android-based systems, providing flexibility and cost-effectiveness. According to market research, the smart POS terminal market is projected to grow significantly, driven by the rising consumer demand for mobility in payment processing. This growth is a testament to the increased popularity of smart pos terminals and android based pos machines, which facilitate swift and secure transactions in various retail settings.
Benefits of Handheld and Mini POS Devices
Handheld and mini POS devices are enhancing customer experiences by allowing transactions anywhere in the store, improving convenience and satisfaction. By using these portable devices, retailers can significantly increase checkout speed, contributing to a more efficient shopping experience. Furthermore, surveys indicate that 70% of customers prefer retailers offering mobile checkout options, demonstrating the consumer demand for such services. Handheld pos machines and mini pos machines not only improve sales reporting and operational efficiency but also elevate the overall shopping journey, creating opportunities for retailers to engage effectively with their customers.
Proactive Fraud Prevention Strategies
Real-Time Monitoring and Suspicious Activity Alerts
Real-time monitoring tools are essential in detecting fraud patterns and generating alerts to mitigate risks instantly. These tools provide continuous surveillance of transaction data, allowing businesses to detect irregularities and respond swiftly to potential threats. According to industry data, businesses that incorporate real-time monitoring systems can achieve a 30% reduction in fraudulent transactions, showcasing their effectiveness in maintaining security. Integration of these tools with existing POS systems can further enhance the fraud detection process. By establishing seamless communication between systems, businesses can ensure more comprehensive protection against unauthorized activities and data breaches.
Role-Based Access Control for Employee Security
Implementing Role-Based Access Control (RBAC) significantly limits access to sensitive information, ensuring it is available only to authorized personnel. This approach not only protects critical data but also correlates with a marked decrease in insider threats. Case studies have shown that businesses employing RBAC systems experience fewer instances of data misuse by employees, as access is strictly governed by the role and necessity. Best practices for setting up RBAC include conducting regular audits and providing employee training. These measures ensure that access roles are up-to-date and that employees understand the importance of maintaining stringent security protocols. Through consistent monitoring and education, businesses can minimize the risk of insider threats and maintain a secure POS environment.
Best Practices to Strengthen POS Security
Regular Software Updates and Patch Management
Keeping your POS software up to date is imperative to safeguard against known vulnerabilities and threats. 90% of successful breaches exploit known vulnerabilities that could have been patched, highlighting the significance of systematic update protocols. An effective approach to patch management involves scheduling updates during low-traffic business hours to minimize disruptions. Prioritizing updates based on risk assessment ensures critical vulnerabilities are addressed promptly, thereby fortifying your POS system against potential attacks. Implementing this routine not only protects your business but also builds customer trust by ensuring their data is secure.
Employee Training on Phishing and Data Handling
Regular employee training on phishing awareness and secure data handling is vital in preventing POS security breaches. Surveys indicate that 80% of data breaches result from employee negligence or lack of awareness, underscoring the need for continuous education. By establishing training programs that include simulated phishing attempts, employees can practice identifying and mitigating these threats in a controlled environment. This proactive approach not only enhances their ability to handle sensitive information securely but also reduces the risk of data breaches, thereby protecting both customer data and the company’s reputation.
Recommended Products
Hot News
-
Smart Card 2019
2024-01-23
-
Trustech 2019
2024-01-12
-
Futurecom 2019
2024-01-12
-
Seamless Payments Asia 2020
2024-01-12
-
Seamless Middle East 2022
2024-01-12

 EN
EN
 AR
AR
 BG
BG
 CS
CS
 DA
DA
 NL
NL
 FR
FR
 IT
IT
 JA
JA
 KO
KO
 PL
PL
 PT
PT
 RU
RU
 ES
ES
 TL
TL
 ID
ID
 LT
LT
 UK
UK
 VI
VI
 HU
HU
 MT
MT
 TH
TH
 TR
TR
 FA
FA
 AF
AF
 MS
MS
 MK
MK
 HY
HY
 AZ
AZ
 KA
KA
 BN
BN
 BS
BS
 LO
LO
 MN
MN
 NE
NE
 ZU
ZU
 MY
MY
 KK
KK
 UZ
UZ
 KY
KY